COVID-19 Data Breaches Used to Fuel Disinformation
The current onslaught of cyberattacks related to the COVID-19 pandemic continued this week. Tuesday night, reports surfaced that attackers publicized over 25,000 emails and passwords from the World Health Organization, The Gates Foundation, and other organizations working to fight the current COVID-19 pandemic. What’s more, this new data dump starkly shows how easily data breaches related to COVID-19 can fuel disinformation campaigns.
The sensitive information was initially posted online over the course of Sunday and Monday, and quickly spread to various corners of the internet often frequently by right-wing extremists. These groups rapidly used the breached data to create widespread harassment and disinformation campaigns about the COVID-19 pandemic. One such group posted the emails and passwords to their twitter page and pushed a conspiracy theory that the information “confirmed that SARS-Co-V-2 was in fact artificially spliced with HIV.”
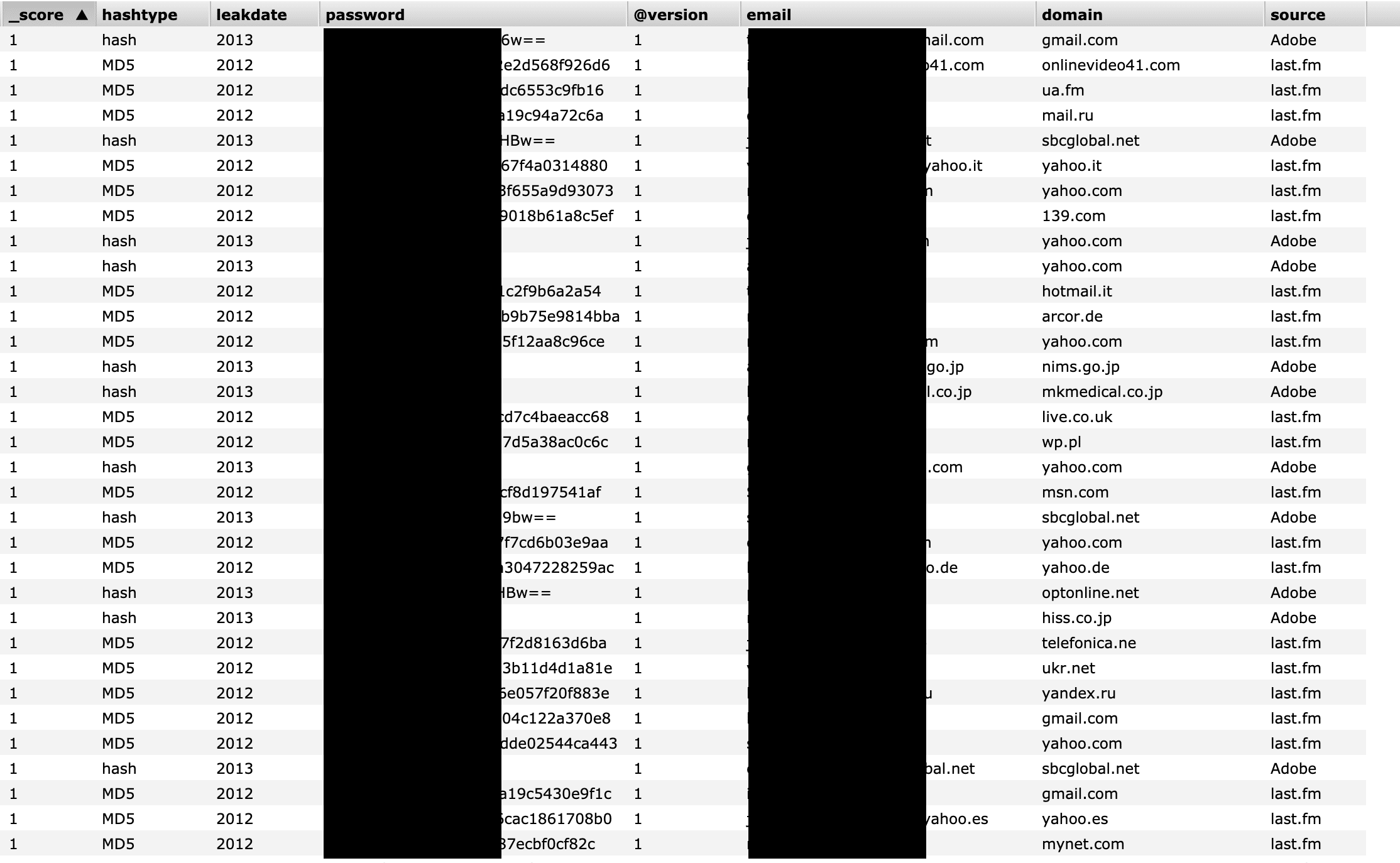
A significant portion of the data may actually be out of date and from previous data breaches. In a statement to The Washington Post, The Gates Foundation said they “don’t currently have an indication of a data breach at the foundation.” Reporting by Motherboard also found that much of the data involved matches information stolen in previous data breaches. This indicates that at least some of the passwords circulating are not linked to the organizations’ internal systems unless employees are reusing passwords.
However, some of the information does appear to be authentic. Cybersecurity expert Robert Potter was able to use some of the data to access WHO’s internal computer systems and said that the information appeared to be linked to a 2016 breach of WHO’s network. Potter also noted a trend of disturbingly poor password security at WHO. “Forty-eight people have ‘password’ as their password,” while others simply used their own first names or “changeme.”
Consequences
Whether the majority of the information is accurate or not, it does not change the fact that the alleged breach has successfully fueled more disinformation campaigns about the COVID-19 pandemic. In the past few weeks, many right-wing extremist groups have used disinformation about the pandemic to spread further fear, confusion in the hopes of seeding more chaos.
This episode starkly shows how data breaches can cause damage beyond the exposure of sensitive information. They can also be weaponized to spread disinformation and even lead to political attacks.