by Doug Kreitzberg | Dec 3, 2021 | Behavior, Cyber Awareness, Human Factor
A recent article in The Wall Street Journal highlights some of the big changes that businesses have made to their employee training programs since the start of the pandemic. Typically, these trainings are formal, multi-hour in-person meetings. According to Katy Tynan, research analyst at Forrester Research, “formal, classroom-delivered training was easy to plan and deliver, but organizations didn’t always see the intended results.” Once the pandemic came along, trainings moved online and offered fun, informal bitesize trainings that employees take overtime. These changes to classical training programs echo many of the behavior-design principles that we incorporate into our cybersecurity awareness training.
Let’s break down some of the key changes the Journal article discusses and how they related to behavior-design principles:
1. Keep it Simple
Instead of hours-long trainings, businesses are starting to break down their trainings into small pieces for employees. In behavior-design terms, this represents an important element towards creating change: making sure users can easily do what we are asking them to do. Simply put, you can’t throw a ton of information at someone and expect them to keep up with it all. What’s more, employees will be a lot more willing to go through with a training if they know it will only take 5 minutes instead of 5 hours. Keeping trainings short and easy to do are therefore important steps towards ensuring that your desired outcome aligns with your employees’ abilities.
2. Consistency is key
Most traditional training programs are a one-and-done deal. Once it’s over, you never have to worry about it again. However, this is exactly what we don’t want employees to take away from training. Instead, consistency is key for any changes. With short lessons, employees can go through the program in small, daily steps that are easy to manage while also keeping the training in their mind over an extended period of time.
3. Make it Interesting
The final piece of the behavioral puzzle is ensuring that employees actually want to do the trainings. Most traditional training programs may involve some small group discussions, but overall employees are shown videos and made to listen to someone talk at them for long periods of time. Employees are only taking in information passively. Instead, trainings should be fun, interesting, and engaging to keep users coming back for more.
The pandemic has brought about so many changes to our lives. While some of the changes have been for the worse, it’s also forced us to start thinking differently about how we do things and come up with creative solutions. The new trend in training programs is one such change. And what makes these changes so successful is the way it incorporates some of the basic behavior-design principles. This is an approach we’ve taken when we developed The PhishMarket™, our cyber awareness training program. By offering engaging and interactive 2-4 minute lessons given daily over an extended period of time, our program has shown success in reducing employee phish susceptibility 50% more than the industry standard.

by Doug Kreitzberg | Dec 16, 2020 | Behavior, Cybersecurity, Privacy
In recent years, much has been made of the privacy paradox: the idea that, while people say they value their privacy, their online behaviors show they are more willing to give away personal information than they’d like to think. Tech giants like Facebook and Google have faced a number of highly public privacy standards, yet millions upon millions of users continue to use these services every day. However, what happens when we think of the value of privacy not in terms of how much we want to protect our privacy, but instead in terms of much we are willing to spend to keep our data private. Newly published research does just that and found that, when looking at the dollar value people place on privacy, there might not be as much as a paradox as we suspected, and business can even learn to leverage the market value of privacy to better understand what they should (and shouldn’t) collect from consumers.
The new study, conducted by assistant professor at the London School of Economic Huan Tang, analyzed how much personal information users in China were willing to disclose in exchange for consumer loans. Official credit scores do not exist in China, so consumers typically have to give over a significant amount of personal information in order for banks to assess their credit. By looking at the decisions of 320,000 users on a popular Chinese lending platform, Tang was able to compare user’s willingness to disclose certain pieces of sensitive information against the cost of borrowing.
The results? Tang found that users were willing to disclosure sensitive information in exchange for an average of $33 reduction in loan fees. While for many in the U.S., $33 may not seem all that significant, $33 actually represents 70% of the daily salary in China, showing users place a significantly high value on their privacy. What’s more, on the bank’s side this translates to 10% decrease in revenue when they require users to disclosure additional personal information.
There are a number of important implications of these study for businesses. For one, it suggests, as Tang says, “that maybe there is no ‘privacy paradox’ after all,” meaning consumers’ online behaviors do, in fact, seem to show a value on protecting people’s right to privacy. While today businesses often utilize the data they collect to make money, by collecting everything and anything they can get their hands on, businesses may be losing significant revenue in lost business. According to Tang, collecting more information than necessary turns out to be inefficient. Instead, business can leverage the monetary value users place on their data to be more discerning when deciding what information to collect. If a piece of data is highly valued by consumers and has little direct economic benefits for a company, it may not be worth collecting. Of course, limiting data is a key tenet of Privacy by Design principles, which organization should be applying to our their practices in order to improve their privacy posture vis-a-vis GDPR and other privacy regulations. Limiting data also improves the organization’s cybersecurity posture because it reduces its exposure.
While it may seem counter intuitive in today’s standard practice of collecting as much data as possible, this study shows that limiting the data that is collected can be, according to Tang, a “win-win” for businesses and consumers alike.
by admin | Nov 3, 2020 | Behavior
For any of us who have lost hundreds of pounds over the years through multiple yo-yo diets will tell you, willpower does not produce lasting change. That’s because willpower requires consistently high motivation over time. Unfortunately, motivation is rarely consistent and certainly not over long periods of time. Willpower is dynamic and episodic. Relying on motivation can perhaps get you started, but not to stay on the path.
Security Awareness programs that focus on punitive approaches to digital behaviors, basically stating that “the beatings will continue until the morale improves” are demonstrating the mirror side of change via motivation, which is intimidation. Like motivation, intimidation is not static, but is dynamic and often yields unintended consequences that damage not only the individual but the enterprise.
Instead, look to increase your ability around the behavior you want to change. Begin by making it easy to do. Help people feel good about themselves when they do it. Build it into their routine.
If you don’t ask for promises, you won’t get pretense. Instead, you will get results.
by Doug Kreitzberg | Aug 14, 2020 | Behavior, Cybersecurity
We’ve talked about the human factors of cybersecurity and the importance of exposing employees to social engineering scams and other attacks that exploit human vulnerabilities. However, when we look at how to improve our organization’s digital practices, we have to do more than train and simulate phish. We have to take a look at what we are asking staff to do and make sure that the cybersecurity behaviors we want them to do are easy, not difficult. Otherwise, those behaviors will become hard to sustain in the long term.
When you’re trying to create new behaviors — for yourself or for your employees — it’s essential to remember that motivation is not a constant. You might be energized and excited to spot phishing emails when you first learn about it, but overtime that could fade. You might get stressed about other parts of your job, or you might be distracted by friends and family, and overtime your interest in your new habit may start to fade. But that is okay! According to behavior scientist BJ Fogg, instead of trying to keep yourself motivated, focus on creating behaviors that are so easy you can do them without worrying about motivation at all.
So, when it comes to fostering cybersecurity behaviors in your employees, it’s essential to keep things short and easy to do. And the truth is, there are a number of super easy cybersecurity behaviors that will help keep you, your employees, and your businesses from being vulnerable to cyber threats. Here are just a few:
Automated Security Scanning
One example of a simple behavior for your software security is to run applications through an automated security scanning tool. Automation is becoming more and more helpful for relieving some of the burden off your IT and security staff. Now, many scanning tools can be set to run automatically, and will highlight potential vulnerabilities with your applications, systems, and even websites. This will leave your security team to evaluate and patch vulnerabilities, instead of wade through your entire system looking for any holes.
Single Sign-On
Another important and easy cybersecurity tool is single sign-on (SSO). Essentially, SSO allows employees to use one set of credentials to access a variety of separate services and applications. While it may seem safer to have different credentials for every applications, single sign-on can actually create stronger authentication processes across the enterprise. As companies began to rely on more and more services, each requiring different credentials, it became hard for employees to keep track of all their log in information, leading to worse password hygiene. By combining all credentials into one, it is easier for employees to use smart and secure credentials.
Phish Reporting
One other easy cybersecurity behavior you can implement is a phish reporting button within your email provider. It’s essential that your IT department is aware of any phishing emails being sent around the office, and in many cases it’s up to the employees to report any phish they receive. While simply forwarding an email to your IT help desk might not seem like a lot, using a simple button to report potential phish is that much easier. Implementing a feature as simple as a report button can increase your reporting and help your IT department keep the network safe.
There are plenty of additional cybersecurity behaviors that you can make easy. All you have to do is first look at what people do, find out what is making the behaviors you want to see difficult to accomplish, then work to make them easier.

by Doug Kreitzberg | Jul 17, 2020 | Behavior
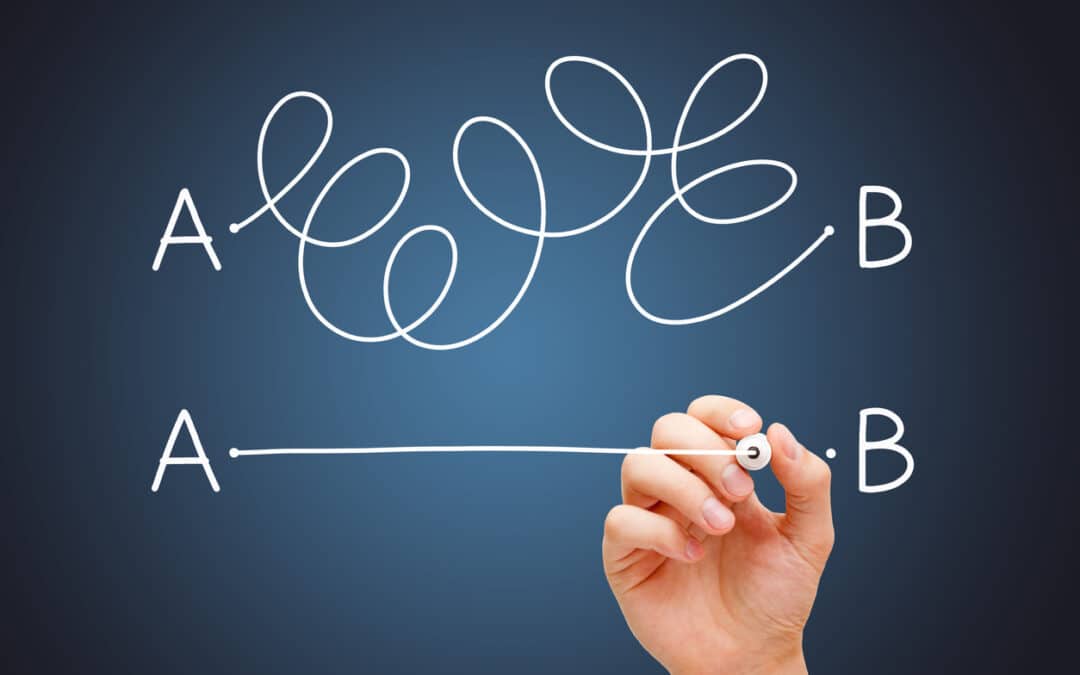
This may seem obvious, but when you are trying to develop new habits and behaviors, one of the biggest areas to consider is your ability to actually do that new habit. If it’s too hard, you won’t be able to sustain the new habit unless highly motivated to do so —which, as we’ve mentioned, is not the right area to focus on. However, the point isn’t that you’ll never be able to learn new skills. The point is to think about ability differently. Instead of thinking that either you can do something or you can’t, breaking ability down into pieces will help you figure out what makes the new habit difficult to do.
When it comes to developing new behaviors, BJ Fogg breaks ability down into six categories that he called the “ability chain”:
- Time Do I have the time to devote to this?
- Money Can I afford to do this?
- Physical Effort Can I physically do this?
- Mental Effort Do I have the mental energy to do this?
- Routine Does the habit fit into my routine or will it require an adjustment?
- Social Is this behavior consistent with my social environment and values?
Once you’ve broken down ability into small chunks, you can start to figure out what exactly your are struggling with. Fogg says to ask the “Discovery Question:” For each link on the ability change ask yourself if that makes the new habit hard to do. Once you identify the ability (or abilities) that make doing this behavior hard, look for ways to make it easier.
Take running as an example. Do you have the time to run a couple times a week? Do you need to buy new shoes or clothes? If so, do you have the money to buy those things? Are you physically able to run? How much mental energy will going for a run take? Does going for a run change your routine too much? Is running consistent with my values? Once you go through the list, you can probably narrow the problem areas down to one or two of the links in the chain and focus on those. So, if my issue is that I can’t physically run for 30 minutes straight, maybe I start by trying to run for 5 minutes straight, then walk for a few minutes, then run for another 5. Then, over time, I’ll build up the strength to run for longer and longer stretches.
At the end of the day, it’s always better to start small in ways that addresses each link in the ability chain. Then you will be in a better position for sustained change over time.